Security in data centers was once defined by a clear boundary, protecting the perimeter, and everything inside could be trusted.
That assumption no longer holds.
In 2026, data centers operate across hybrid environments, edge locations, and multi-cloud platforms, with workloads constantly moving between them. At the same time, access points have multiplied: APIs, remote users, third-party integrations, and automated systems, all interacting with critical infrastructure. This has fundamentally expanded the attack surface, making traditional perimeter-based defenses increasingly ineffective.
The challenge is not just more threats, but less visibility and control. Once an attacker gains access, lateral movement within the network can go undetected in architectures that still rely on implicit trust. This is particularly critical as data centers now support sensitive AI workloads, real-time processing, and distributed applications.
Security models built on “trust but verify” are being replaced by a stricter principle:
Never trust, always verify.
Zero-trust architecture is emerging not as an upgrade but as a necessary shift in how data center security is designed and enforced.
Is Perimeter Security Still Relevant in Modern Data Centers?
Perimeter-based security was built on a simple assumption: everything inside the network can be trusted. That model is increasingly breaking down.
Modern data centers no longer operate within fixed boundaries. Hybrid cloud, edge deployments, and API-driven architectures have dissolved the traditional perimeter, replacing it with a distributed and dynamic attack surface. According to IBM’s Cost of a Data Breach Report 2024, over 80% of breaches involve data stored across multiple environments, highlighting how fragmented infrastructure increases exposure.
Data Breaches by Environment Type (2025-2026 Benchmarks)
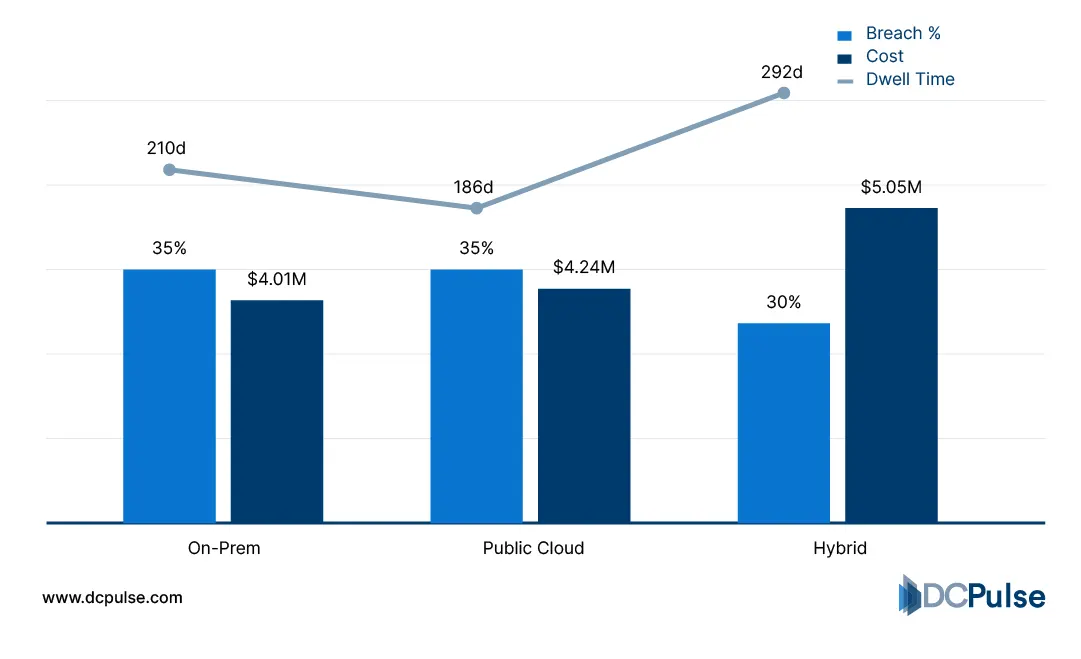
The risk is not just external attacks, but lateral movement within the network. Once inside, attackers can move across systems if internal trust assumptions remain intact. The Cybersecurity and Infrastructure Security Agency emphasizes that traditional perimeter defenses are insufficient against modern threats, especially in environments with distributed access points.
Another challenge is identity sprawl. Users, services, and machines now interact across multiple environments, making identity the new security boundary. Research from Gartner suggests that identity-based attacks are among the fastest-growing threat vectors in enterprise environments.
Growth of Identity-Based Attacks (2025–2026 Benchmarks)

What this reveals is a structural shift.
Perimeter security is not disappearing, but it is no longer sufficient on its own. In modern data centers, trust cannot be assumed based on location; it must be continuously verified at every access point.
What Does Zero-Trust Actually Change Inside the Data Center?
Zero-trust does not add another security layer; it redefines how trust is established across the entire data center.
At its core, zero-trust shifts security from network location to identity and context. Every user, device, and workload must be authenticated and authorized continuously. The National Institute of Standards and Technology (NIST SP 800-207) defines zero-trust as eliminating implicit trust and enforcing verification for every access request.
A key architectural change is microsegmentation. Instead of securing the network as a whole, zero-trust isolates workloads into smaller segments, restricting lateral movement. Guidance from the Cybersecurity and Infrastructure Security Agency highlights segmentation and granular access control as core components of zero-trust implementation.
Zero-trust also introduces continuous verification. Access decisions are dynamically evaluated based on user behavior, device posture, and risk signals rather than granted once. Microsoft’s zero-trust security model emphasizes continuous monitoring and validation across sessions.
Traditional vs. Continuous Verification (2026)
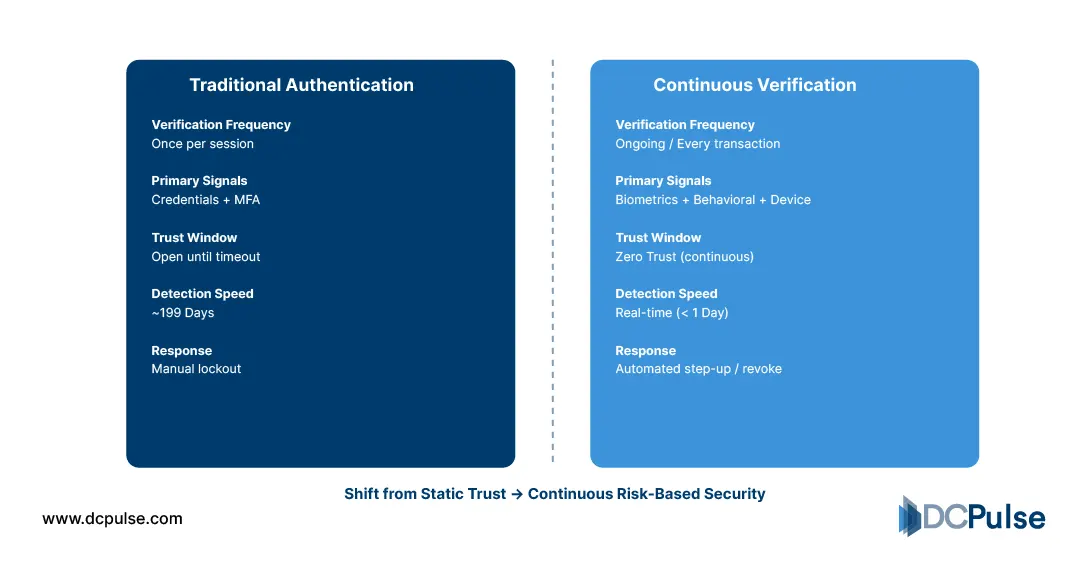
Finally, zero-trust enforces workload-level security, ensuring applications authenticate directly with each other instead of relying on network trust boundaries.
The shift is clear:
Security moves from perimeter defense to continuous, identity-driven control over every interaction within the data center.
Who Is Leading the Shift to Zero-Trust Architectures, and How?
The shift to zero-trust is no longer theoretical; it is being institutionalized by governments, hyperscalers, and enterprise security leaders.
At the policy level, the U.S. federal government has made zero-trust a mandate. The White House’s Executive Order on cybersecurity requires federal agencies to adopt zero-trust architectures, accelerating adoption across critical infrastructure sectors. The Cybersecurity and Infrastructure Security Agency has since formalized a Zero Trust Maturity Model to guide implementation.
Zero Trust Adoption Roadmap: Core Milestones (2021-2026)
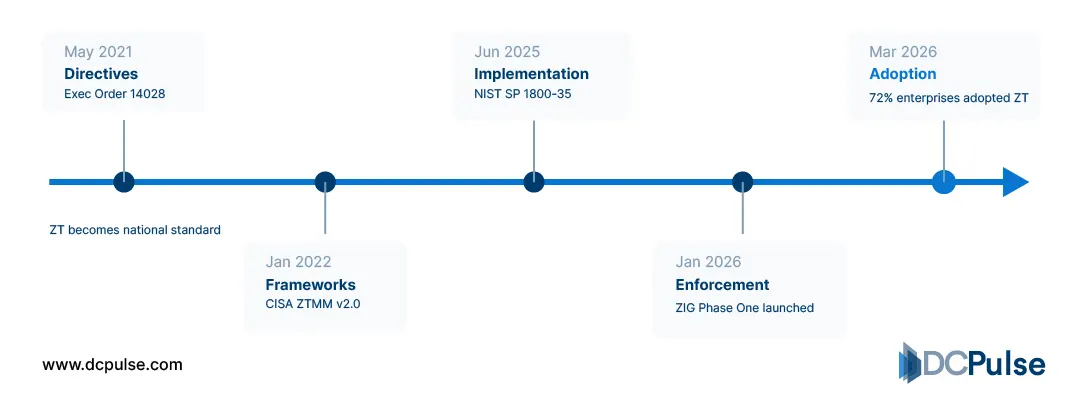
Hyperscalers are operationalizing zero-trust at scale. Google pioneered the BeyondCorp model, which removes reliance on network location for access control and enforces identity-based security across distributed systems. This model has become a reference architecture for zero-trust deployments.
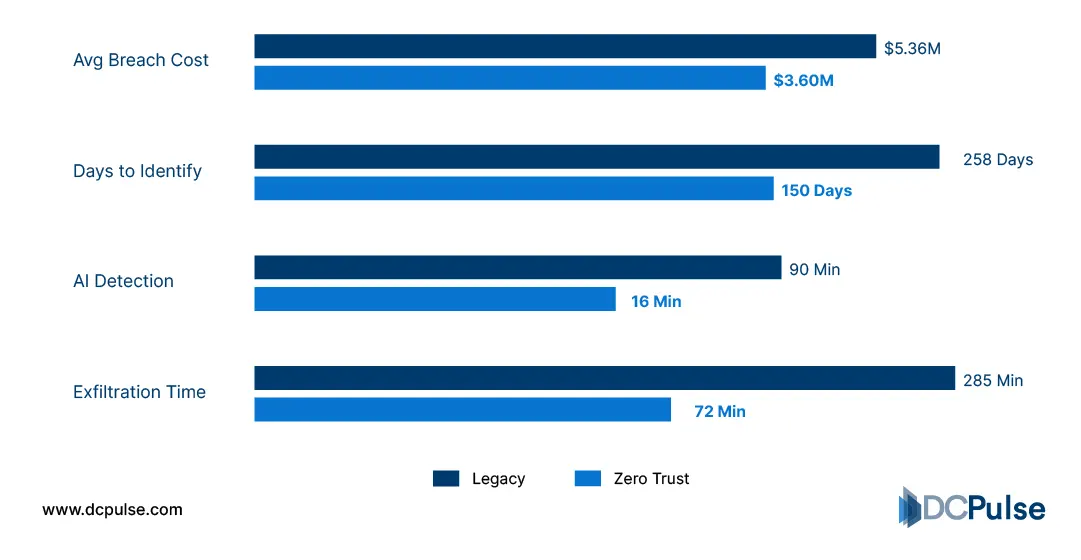
Enterprise adoption is also accelerating. According to IBM’s security research, organizations implementing zero-trust strategies experience significantly lower breach costs compared to those that do not, reinforcing its business value.
Zero Trust Financial & Operational Impact (2025-2026)
Technology vendors are aligning their platforms around zero-trust principles, integrating identity, endpoint security, and network controls into unified architectures. This reflects a broader industry shift from isolated security tools to integrated, policy-driven security frameworks.
The key shift is this:
Zero-trust is no longer an optional framework; it is becoming a baseline requirement enforced by policy, proven by practice, and adopted at scale.
Is Zero-Trust Becoming Mandatory for Data Center Security?
Zero-trust is no longer just a best practice; it is rapidly becoming a baseline requirement for securing modern data centers.
As infrastructure becomes more distributed and attack surfaces expand, traditional security models are proving insufficient. Zero-trust addresses this by enforcing continuous verification and eliminating implicit trust, making it well-suited for environments where users, workloads, and data constantly move across boundaries.
However, adoption is not without challenges. Implementing zero-trust requires significant changes to existing architectures, including identity management, network segmentation, and policy enforcement. It also introduces operational complexity, particularly for organizations with legacy systems and fragmented environments.
What is emerging is not a complete replacement of existing security models but a layered evolution. Organizations are integrating zero-trust principles into their infrastructure while maintaining elements of traditional security where necessary.
The direction, however, is clear.
Zero-trust is shifting from a strategic initiative to an operational necessity, driven by both threat realities and regulatory pressure. In an environment where trust can no longer be assumed, the ability to verify every interaction is becoming fundamental to how data centers are secured.